Resetting the Windows administrator’s password or Linux root account password is a common troubleshooting practice when faced with systems infected with mailware, data corruption, and system recoveries. This article does not prompt malicious use, but instead stress the point that an account password does not protect your data.
In principle, passwords are stored locally, anything stored locally can be obtained and modified by slaving that physical data. For example, a hard drive can be removed, added to a different computer already running it’s own OS. That drive will now show up as a slave drive and the contents easily accessible. The following tutorial does not use any third party tools, and only relies on the initial media used to install the OS.
- Resetting Stock Windows Administrator password using Installation Disc
- Resetting Non-Stock Administrator Password using Windows Installation Disc
- Resetting Linux Root Password using Single User Mode

Resetting Stock Windows Administrator password using Installation Disc
This method will only work if you have not touched the stock Administrator account that comes with a fresh install of windows 7. By default the Administrator account with a blank password and disabled. In this method we will take advantage of this by enabling the Administrator account via the registry. If you set the built-in Administrator account for your Windows rollouts or your home Windows machines I give you kudos for being a smart user and follow best practices in locking down your computer. However it does add an extra step in resetting the Administrator’s password. But, No problem!
The following two sceniors make use of the Window Installation Disk.
Windows 7 32-bit Professional Installation Disc
**md5
Windows 7 64-bit Professional Installation Disc
**md5
- Boot into your Windows Installation Disk
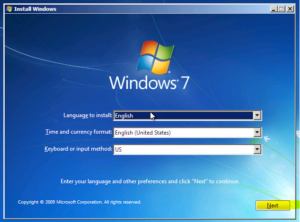



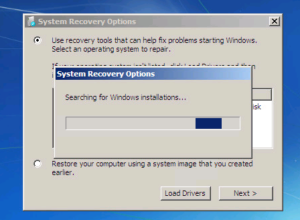
- Click Next, and wait for Recovery to scan for Windows OS’s
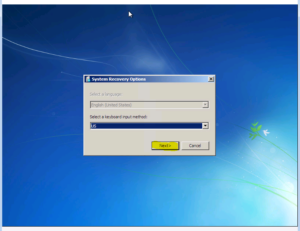


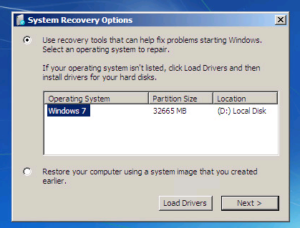
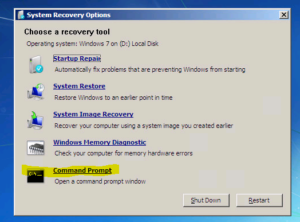
- Click the Windows OS you want and click next. This will bring you to the Recovery Options list. Click command prompt.


- Once command prompt opens, type regedit

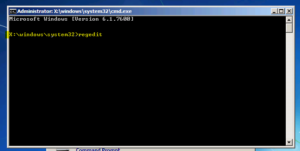
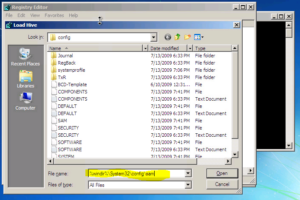
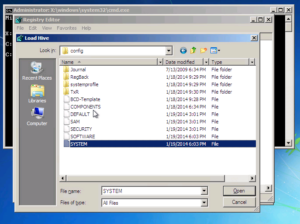
- Regedit will open, click on HKLM, then click File –> Load Hive. Now we need to navigate to the system SAM file located usually D:\Windows\System32\config\SAM ,since C: is the reserved partition Windows 7 makes. If this is not the case you will have to use diskpart on the command line to figure out which drive letter to use.

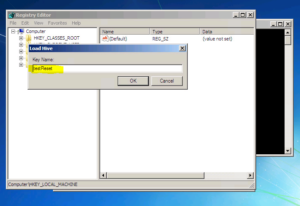
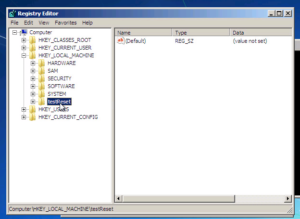
- Give the Loaded Hive a name, this can be anything. I named my testReset. It will now show up in the Registry list.


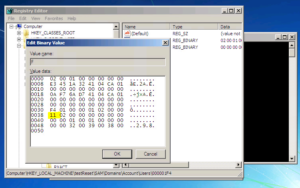
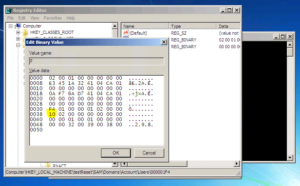
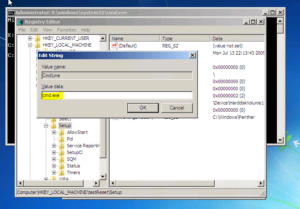
- In this new Hive List, browse to {testReset} –> SAM –> Domains –> Account –> Users –> 000001F4 and modify the Key F4

- Locate the hex 11 bit and change it to 10 and click OK and this will activate the stock administrator account that is currently disabled.


- Restart the system and you should see the Administrator account at the Login Prompt.


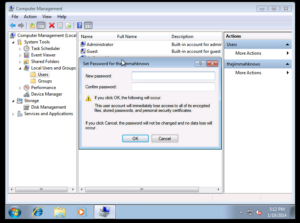
- Log into the Administrator and use Computer Management to set the password of your account.

Resetting Non-Stock Administrator Password using Windows Installation Disc
- Repeat Steps 1-4 from the first method.
- We need to load a Registry Hive from the system we are trying to reset the password for. In this case SYSTEM instead of SAM, located D:\windows\system32\config\SYSTEM ,since C: is the reserved partition Windows 7 makes. If this is not the case you will have to use diskpart on the command line to figure out which drive letter to use.

- Navigate to the Registry key SetupType located under testReset –> Setup –> SetupType. Modify this DWORD value from 0 to 2 and click OK

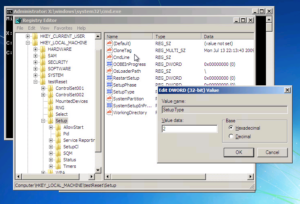
NOTICE: A value of 2 will run the value located in the CMDLine registry key. Value 0 =does nothing and shows the login screen at boot. Value 1 = Runs the value located in CMDLine registry key, but then Restarts. - Edit the registry value of CMDLine

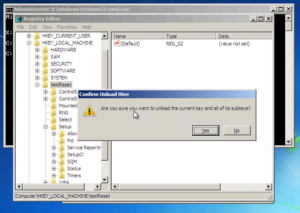
- Unload the tesetReset Hive. Click on testReset then click File –> Unload Hive.

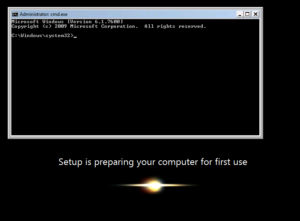
- Restart the system, you will be presented with the following command prompt

- Now set the Administrator Password via the syntax net user Administrator {passwd}

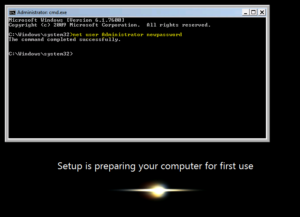
- Type exit, and you should be presented with the Login Screen. Try the password you just set!!!


Resetting Linux Root Password using Single User Mode
- Reset the system and enter editor mode of your Boot loader. In my case Grub. Select the boot line and hit ‘e’

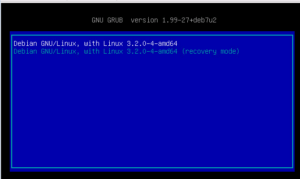
- Find the Linux/Kernel Line:

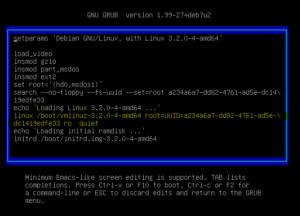
- Add single init=/bin/bash to the end of the kernel or linux line(depends on your version.

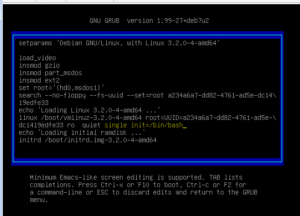
- Boot the changes we just made. In my case and version of grub F10 boots the changes, check with your boot loader, it should be written at the bottom of the editor. As you can see we are dropped into a read only root shell. If
 If you try to reset the password now you will receive this error:
If you try to reset the password now you will receive this error:

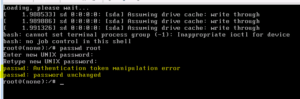
- The filesystem will be set in read only mode, which does not allow us to manipulate the password user file. To remedy this do the following to mount the volume as read/write
# mount -rw -o remount / # passwd root # ***** # ***** - Repeat the passwd reset procedure again
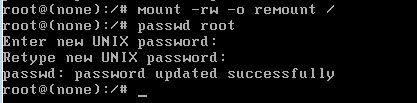
- Verify
Now restart the system and try to log in as root with the password you just set
Thoughts
I hope this article is both helpful and informative. We can see from this article that physical security (the ability to physically obtain) your data is very important. Regardless of the password strength you choose. There are also preventative measures to take in tandem with a strong password. Some preventative measures we can utilize are are free are:
- Windows users can use BitLocker, a free drive encryption software built into windows to prevent a third party or bootable media obtaining or modifying the password file.(SAM file).
- Windows users can use TrueCrypt, a OpenSource drive encryption software.
- Linux users can encrypt GRUB, see this article.
- Linux users can also use open source drive encryption to prevent third party or bootable media from obtaining or modifying the password file.(/etc/passwd)
Sources
- http://answers.microsoft.com/en-us/windows/forum/windows_7-security/how-do-i-reset-my-forgotten-administrators/945fcc2f-e10c-45ac-9a7f-cd4c328dd063
- http://www.sevenforums.com/tutorials/85657-password-reset.html
- http://answers.microsoft.com/en-us/windows/forum/windows_7-windows_install/where-can-i-download-windows-7-iso-i-have-a/7d964b05-2be9-4800-bc7f-3ca30356fc3d